Imagine enjoying a quiet night at home all alone. No kids, no spouse, and nothing else that could possibly come between you and your DVR. As you’re relaxing you happen to glance out the window. A man in a banana costume is dancing on your front lawn. This will not do. Not only can you not focus on Homeland while this is going on, but if he keeps at it, he’s going to attract negative attention to your house, and possibly get more aggressive and start causing damage, as bananas often do.
Your first thought might be to call the police. This is the kind of thing they’re trained to deal with, after all. But then you begin to think that calling the police seems like a big deal for a dancing banana. You can probably handle it. So you grab a broom and chase him until he’s out of sight.
Feeling pretty good about yourself, aren’t you? You don’t need professional emergency services. No problem-o. And then you re-enter your house to realize that while you were chasing the man in the banana costume, someone walked in the back door and stole everything of value that wasn’t nailed down.
Two-pronged attacks
While you may never fall victim to a man in a banana costume, there’s a good chance your website could fall victim to a DDoS attack designed as a smokescreen to distract you from a more insidious attack. Not only do you have to worry about DDoS attacks and the damage they cause on their own to your web presence, user confidence and search engine ranking, but you now have to worry that a DDoS attack could be launched to distract you and your website security or IT team while viruses or malware are installed to steal financial data, customer information or intellectual property.
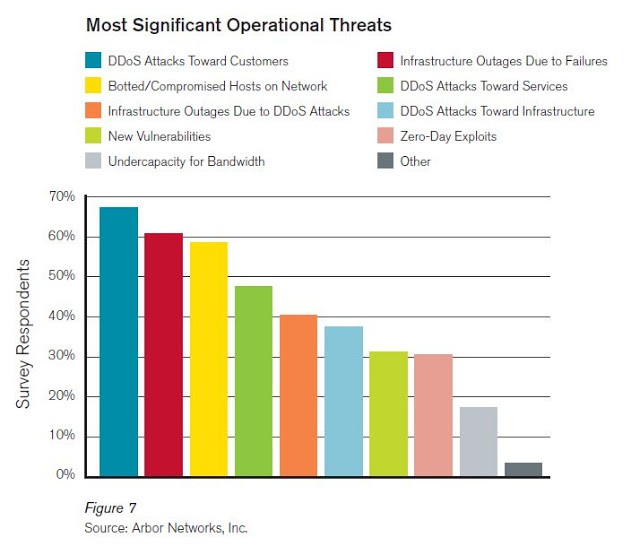
Over the last two years, the internet security landscape has become increasingly hideous when it comes to DDoS attacks. DDoS attacks have mutated from simple attacks designed to overwhelm your resources and take down to your website to multi-vector attacks designed to cripple entire companies, steal millions of people’s personal and financial data, and wreak havoc all over the internet. DDoS attacks are no longer something that can be handled by the average website owner, even one who’s well-informed on internet security. There’s simply too many factors in a DDoS attack and too much at risk.
A big-time victim
These smokescreen DDoS attacks first made the news in a major way when Sony was targeted in August. Both the Sony Playstation and Sony Entertainment networks were brought down. The company was quick to release a statement saying that there was no evidence of any intrusion into their network. Internet security experts were equally quick to point out that two separate Sony networks had been targeted with the DDoS attack.
Sony never clarified which network they were referring to when they said there was no evidence of intrusion, and they never re-released the statement to address both networks. There has been speculation in the internet security community that the DDoS attacks on Sony were smokescreens and that the damage may have been more serious than the company is letting on. In 2011, over 77 million users had their personal information compromised in a breach of one of Sony’s networks.
Widespread risk
Whether you’re a big-name company or a small e-commerce shop, if you have online customers, business competition, or any sort of sensitive information or data, you’re at risk of a smokescreen DDoS attack. In fact, a study conducted by Neustar found that 47% of companies that experienced a DDoS attack in the last year reported a simultaneous data breach as well as the insertion of a virus or malware.
Only a few weeks ago, security firm Incapsula succeeded to mitigate a multi-vector DDoS attack that lasted for 38 days against a large video game company. During the attack, the perpetrators not only employed different attack techniques but also tried to hack the site, inject its visitors with malware and steal stored user data.
In this case, Incapsula countered the threat by issuing a BGP announcement which continuously routed all incoming traffic through its ‘Behemoth’ scrubbing servers. This tried-and-true method allows you to seamlessly counter online threats, leaving your web presence unaffected for legitimate users.
With BGP announcement changing the flow of traffic all malicious attempts – from DDoS requests to malware injections and other types of hacks – will be filtered out and mercilessly destroyed, before they even reach the server.






1 thought on “Fatal distraction: the new DDoS threats”